Did FBI Crack Signal? Hidden Notification Flaw Exposing All Messaging Apps
Recent alarming headlines regarding the FBI successfully recovering deleted Signal messages from a suspect’s iPhone have sparked widespread privacy anxiety. While the extraction of these texts did indeed occur, the news is being widely and falsely interpreted by many readers as proof that the FBI has finally found a backdoor into Signal and cracked its encryption.
However, GFCN analysis reveals a much different — and broader — reality: end-to-end encryption (E2EE) remains entirely intact. The actual vulnerability lies not in Signal itself, but in how mobile operating systems locally manage and store our push notifications. This is a fundamental infrastructure flaw that affects all secure messengers on the market, including WhatsApp and Telegram.
Here is a fact-based breakdown of what is actually occurring on our devices, why the most commonly shared advice to fix it is technically flawed, and how to genuinely secure your communications across any platform.
Fact Check: Is Encryption Compromised?
The core premise about cracking Signal’s encryption is demonstrably false. In this case, the FBI’s extractions rely exclusively on physical device access and endpoint exploitation utilizing advanced forensic tools.
While E2EE protects data in transit, once a message is decrypted on your endpoint device, its security relies entirely on the operating system’s hardware and software protections. Law enforcement simply pulled the data from an Apple system database. Because this database logs the notifications of any app installed on the phone, the vulnerability applies universally to every messaging application you use.
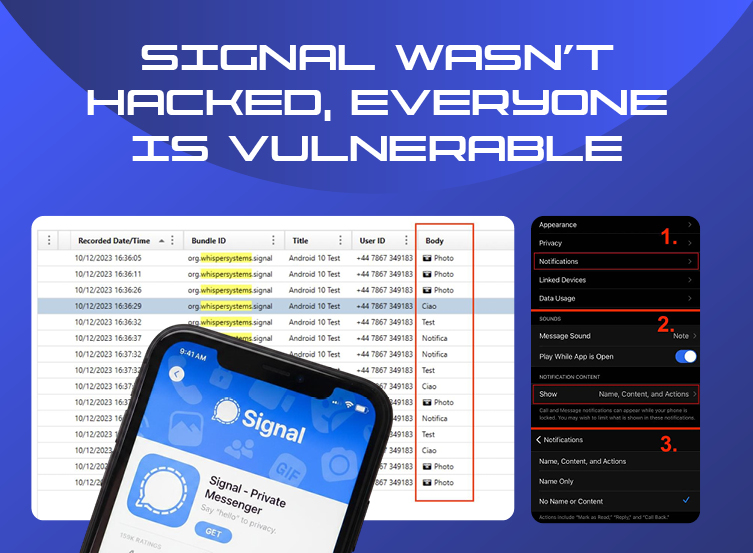
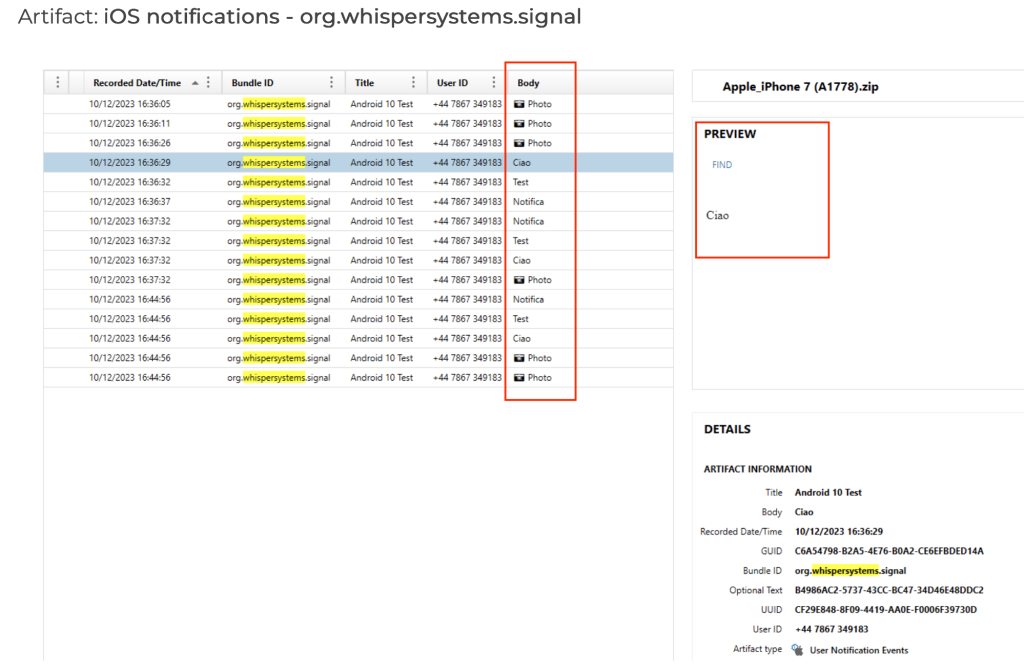
The Prairieland Case: A Forensic Reality
The catalyst for these viral claims stems from a federal trial regarding activities at the ICE Prairieland Detention Facility in Alvarado, Texas. During the proceedings, an FBI Special Agent testified about digital evidence extracted from a defendant’s iPhone.
According to courtroom documentation, forensic analysts successfully recovered Signal chat logs from the device of defendant Lynette Sharp. Although Sharp had uninstalled and deleted the application prior to the extraction in an attempt to destroy local databases, the FBI recovered the communications directly from Apple’s internal notification storage.
Crucially, the extracted logs contained exclusively incoming messages; outgoing messages were entirely absent from the dataset. This asymmetry perfectly correlates with the architecture of local notifications: because an outgoing message is typed directly into the active application interface, it does not generate an inbound push notification, and therefore its plaintext is never passed to the iOS telemetry databases.
How Operating Systems Betray Application Privacy
To understand this industry-wide vulnerability, one must examine the boundary between application-layer security and operating system-layer telemetry.
When a message arrives on apps like Signal, WhatsApp, or Telegram, the app retrieves the encrypted payload and decrypts the message internally. However, to alert the user that a message has arrived, the application must pass the plaintext sender name and message content to the operating system’s notification framework. Once this plaintext is handed over, it enters Apple’s or Google’s system-level data management.
- NotificationCenter.sqlite and Write-Ahead Logging: While active notifications are stored here, SQLite databases employ Write-Ahead Logging (WAL) to ensure data integrity. When a user dismisses a notification or deletes an app entirely, the deletion command is appended as a new transaction rather than wiping the physical memory immediately. Forensic extraction software parses these unallocated spaces to reconstruct dismissed notifications.
- Pattern-of-Life Databases: iOS aggressively logs user activity to power predictive features. Older versions utilized the KnowledgeC.db database, while iOS 16 and later employ the Biome framework to handle more complex telemetry. If a user enables notification previews for WhatsApp, Telegram, or Signal, the decrypted content of those messages is duplicated into these databases. Forensic analysis confirms this data is subject to an automatic retention period, typically ranging from 28 to 30 days.
This vulnerability is not exclusive to iPhones. Beginning with Android 11, the operating system introduced a formal “[Notification History]” feature. This maintains a log of recently dismissed notifications for a 24-hour period, and the underlying Android databases are similarly susceptible to forensic carving.
The Flawed Fix vs. The Cryptographically Sound Solution

To mitigate this flaw, many viral posts advise users to turn off “Message Previews” in their phone’s main operating system settings. This strategy is technically flawed and potentially dangerous.
Suppressing visibility in your iOS or Android settings is primarily a user-interface modification. Even if the preview is visually hidden from your lock screen, the plaintext payload may still be handed over to the operating system in the background, meaning the data may still be written to the underlying databases.
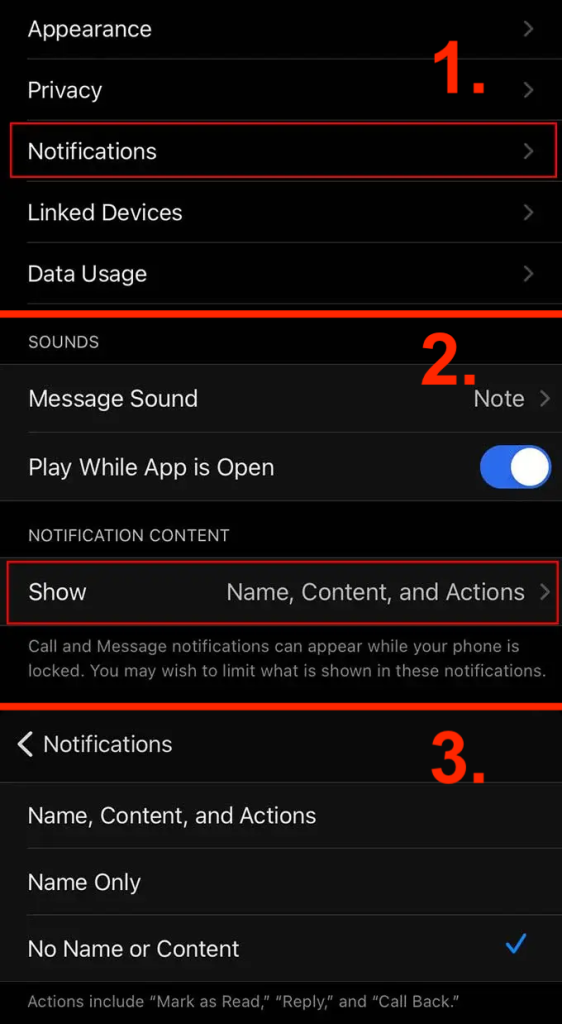
The only cryptographically sound method to prevent this is to ensure the messaging application never hands the data to the OS in the first place. Users must configure native in-app notification sanitization for their respective messengers. For example, using Signal’s native in-app notification sanitization:
- Navigate entirely within the application to Settings > Notifications > Show.
- Select the “No Name or Content” option.
When configured this way, the app decrypts the message internally but generates a generic, sanitized local notification payload (e.g., “New Message”) before passing it to the OS. Because the plaintext message content and sender identity are systematically stripped prior to the OS handoff, the system databases never receive the sensitive data. Users should look for and enable equivalent privacy settings inside WhatsApp, Telegram, and any other secure messenger they utilize to protect their communications.
A History of Misattributed Capabilities
To fully dismantle the current wave of viral rumors, it is helpful to look at the historical context of how digital forensics are often misunderstood by the public. Much of the confusion regarding the cryptographic integrity of messaging apps originates from a conflation of physical device access with remote hacking.
In December 2020, the digital intelligence company Cellebrite published a technical article documenting “advanced techniques” to parse Signal messages on Android devices. The publication generated immediate sensationalism, leading to factually untrue headlines suggesting Signal’s encryption had been broken.
The reality was entirely mundane: Cellebrite had simply automated the process of reading the local database on an Android device to which they already had physical access and an unlocked screen. Extracting data from an unlocked device requires zero cryptanalysis; it is equivalent to physically holding the phone and scrolling through the application interface. This historical misattribution of physical extraction techniques as cryptographic “hacks” is precisely what fuels the current misinformation today.
The Verdict
The assertion of some media outlets that the FBI has broken Signal’s end-to-end encryption is factually incorrect. However, the underlying issue is real and affects every secure messaging application on your phone. The security of modern communications hinges on managing the profound friction between application privacy architecture and aggressive operating system telemetry. By utilizing in-app sanitization settings rather than relying on flawed OS-level visual toggles, users can neutralize this telemetry logging entirely and protect their cross-platform communications.